 Whereas BitTorrent consumer performance hasn’t essentially modified over the previous 20 years, builders of main purchasers haven’t let their software program stagnate.
Whereas BitTorrent consumer performance hasn’t essentially modified over the previous 20 years, builders of main purchasers haven’t let their software program stagnate.
An excellent instance is the superb qBittorrent, a feature-rich open supply consumer which nonetheless receives common updates. In frequent with related purchasers, qBittorent may be discovered on GitHub together with its supply and set up directions.
Elsewhere on the identical platform, customers had been lately making an attempt to work out how a normal qBittorrent set up all of the sudden led to the looks of undesirable cryptocurrency mining software program on the identical machine.
Proxmox and LXC
For these unfamiliar with Proxmox VE, it’s an surroundings for digital machines that when tried turns into very helpful, extraordinarily rapidly. It’s additionally free for mere mortals and in most circumstances, very straightforward to put in and stand up and working.
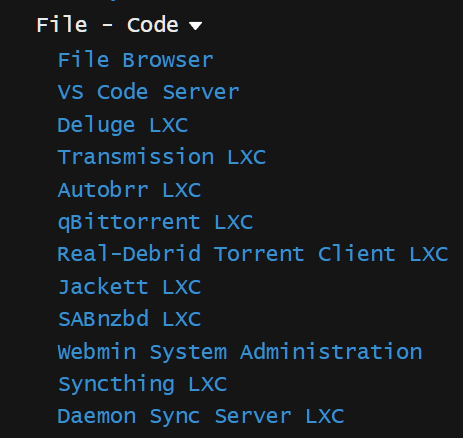 With assist from numerous Proxmox ‘helper scripts’ supplied by tteck on GitHub (small pattern to the correct), even rookies can set up any of dozens of obtainable software program packages in a matter of seconds utilizing LXC containers.
With assist from numerous Proxmox ‘helper scripts’ supplied by tteck on GitHub (small pattern to the correct), even rookies can set up any of dozens of obtainable software program packages in a matter of seconds utilizing LXC containers.
Even when none of that is sensible, it doesn’t matter. Those that need qBittorrent put in, for instance, can copy and paste a single line of textual content into Proxmox…and that’s it. On condition that the entire course of is sort of all the time flawless, consumer points are very uncommon, so to listen to of a doable malware an infection got here as an actual shock lately
Cryptominer Discovery
In abstract, a Proxmox consumer deployed a tteck script to put in qBittorrent after which a month later discovered his machine being labored onerous by cryptomining software program often called xmrig. Whereas he investigated the issue, tteck eliminated the qBittorrent LXC script as a primary precaution, but it surely quickly turned clear that neither Proxmox or tteck’s script had something to do with the issue.
The unwelcome software program was certainly put in maliciously, however attributable to a collection of avoidable occasions, moderately than a genius hack.
When a qBittorrent set up like this completes and the software program is launched, entry to qBittorent takes place via an online interface accessible from most internet browsers. By default, qBittorrent makes use of port 8080 and since many customers wish to entry their torrent purchasers from distant networks, qBittorrent makes use of UPnP (Common Plug and Play) to automate port forwarding, thereby exposing the online interface to the web.

Having this working in file time is all very good, however that doesn’t imply it’s protected. To make sure that solely the operator of the consumer can entry the online interface, qBittorrent permits the consumer to configure a username and a password for authentication functions.
This typically implies that random passers-by might want to possess these credentials earlier than having the ability to do harm. On this case, the default admin username and password weren’t modified and that allowed an attacker to simply entry the online interface.
Attacker Informed qBittorrent to Run an Exterior Program
To permit customers to automate numerous duties associated to downloading and organizing their information, qBittorrent has a function that may robotically run an exterior program when a torrent is added and/or when a torrent is completed.
The choices listed below are restricted solely by the creativeness and talent of the consumer however sadly the identical applies to any attacker with entry to the consumer’s internet interface.

On this case the attacker informed the qBittorrent consumer to run a primary script on completion of a torrent. The script accessed the area http://cdnsrv.in from the place it downloaded a file known as replace.sh after which ran it. The results of which are defined intimately by tteck, however the details are a) unauthorized cryptomining on the host machine and b) the attacker sustaining root entry by way of SSH key authentication.
Simply Prevented
The default admin username for qBittorrent is ‘admin’ whereas the default password is ‘adminadmin’. Had these common-knowledge defaults been modified following set up, the attacker would nonetheless have discovered the online interface however would’ve had no helpful credentials for standard entry.
Extra essentially, possession of the proper credentials would’ve had restricted worth if the qBittorrent consumer hadn’t used UPnP to show the online interface within the first place. Taking one other step again, if UPnP hadn’t been enabled within the consumer’s router, qBittorrent would’ve had no entry to UPnP, and wouldn’t have been capable of ahead ports or expose the interface to the web.
In abstract: disable UPnP within the router and solely allow it as soon as its operate is absolutely understood and when completely mandatory. By no means depart default passwords unchanged, and if one thing doesn’t must be uncovered to the web, don’t expose it unnecessarily.
Lastly, it’s price mentioning that tteck‘s response, to an issue that had nothing to do with Proxmox or his scripts, has been top notch. Anybody putting in the qBittorrent LXC from right here will discover the default admin password modified and UPnP disabled robotically.
Any time saved may be spent on automated installs of Plex, Tautulli, Emby, Jellyfin, Jellyseerr, Overseerr, Navidrome, Bazarr, Lidarr, Prowlarr, Radarr, Readarr, Sonarr, Tdarr, Whisparr, and plenty of, many extra.
